Head over to our on-demand library to view sessions from VB Transform 2023. Register Here
The potential for supply chain attacks has grown as cybercriminals become increasingly adept at exploiting the dependencies within software services containing open-source libraries. But companies haven’t moved fast enough to take adequate counter measures.
This was highlighted by Chris Krebs, the inaugural director of the U.S. Cybersecurity and Infrastructure Security Agency (CISA), in his keynote address at the BlackHat conference.”Companies shipping software products are shipping targets,” Krebs warned the audience, a sentiment echoed by the White House’s recent announcement of a national cybersecurity strategy that emphasizes cyber-resilience and holds software companies accountable for the security of their products.
Security gets traded for speed – even with new ML model development
DevOps teams are under pressure to deliver more apps that contain ML models in less time to support new sources of digital-first revenue and customer experiences. DevOps leaders say that security gate reviews get sacrificed to meet increasingly tight code delivery dates. VentureBeat has learned that a typical DevOps team in a $600 million enterprise has over 250 concurrent projects in progress, with over 70% dedicated to safeguarding and improving digital customer experiences.
Security gets traded for speed because nearly every DevOps team has a backlog of new digital transformation apps supported by ML models that are behind schedule. Security testing apps are also disconnected from DevOps, and engineers aren’t trained to embed security into their code during development. Using open-source code saves time and keeps development within budget but introduces new risks. 97% of commercial code contains open-source code, and 81% contains at least one vulnerability. Additionally, 53% of the codebases analyzed had licensing conflicts, and 85% were at least four years out of date.
Event
VB Transform 2023 On-Demand
Did you miss a session from VB Transform 2023? Register to access the on-demand library for all of our featured sessions.
JFrog’s latest release goes all-in on protecting ML models during the development
JFrog, a leader in providing software supply chain security for DevOps, knows these and other challenges well. Today, the company launched a series of new products and enhancements at its 2023 swampUP Conference. The most noteworthy announcements are in ML Model Management, including scanning models for compliance, detecting malicious models, and managing model delivery alongside software releases.
“Today, Data Scientists, ML Engineers, and DevOps teams do not have a common process for delivering software. This can often introduce friction between teams, difficulty in scale, and a lack of standards in management and compliance across a portfolio,” said Yoav Landman, Co-founder and CTO, JFrog. “Machine learning model artifacts are incomplete without Python and other packages they depend on and are often served using Docker containers. Our customers already trust JFrog as the gold standard for artifact management and DevSecOps processes. Data scientists and software engineers are the creators of modern AI capabilities, and already JFrog-native users. Therefore, we look at this release as the next logical step for us as we bring machine learning model management, as well as model security and compliance, into a unified software supply chain platform to help them deliver trusted software at scale in the era of AI.”
The company also introduced a new security platform that provides end-to-end protection across the software development lifecycle (SDLC), from code to runtime. New features include SAST scanning, an OSS catalog as part of JFrog Curation, and ML model security. Additional new capabilities include release lifecycle management to track software bundles and enhanced DevOps features like immutable release bundles.
JFrog’s strategy is focused on unifying and streamlining the entire software development lifecycle within a single platform. As evidenced by their results at Hitachi Vantara, JFrog Artifactory acts as a “single source of truth” to manage software binaries and artifacts across the organization while providing consistent security scanning with JFrog Xray. By replicating key repositories across multiple sites, JFrog enabled Hitachi Vantara to accelerate multi-site pipelines and shift security left.

Getting scaling right is core to securing every phase of ML model development
What’s noteworthy about JFrog’s series of announcements today is how they’re building out security and code integrity from the initial commit of source code through building, testing, deployment, and runtime operations of ML models.
“It can take significant time and effort to deploy ML models into production from start to finish. However, even once in production, users face challenges with model performance, model drift, and bias,” said Jim Mercer, Research Vice President, DevOps & DevSecOps, IDC. So, having a single system of record that can help automate the development, ongoing management, and security of ML Models alongside all other components that get packaged into applications offers a compelling alternative for optimizing the process.”
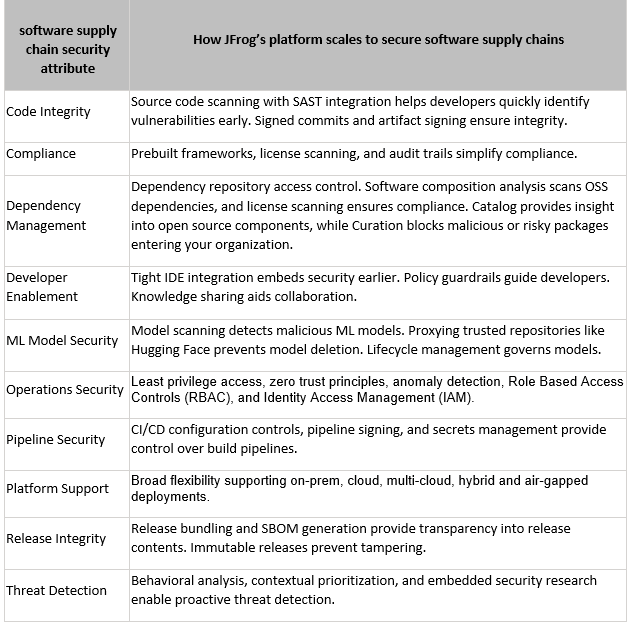
JFrog’s DevOps, engineering, and product management teams deserve credit for integrating AI/ML techniques to improve compliance, coding, developer productivity, and threat detection in their platform, strengthening those elements in the latest release. The following table compares JFrog’s progress in delivering solutions that scale across core software supply chain security attributes CISOs, CIOS, and boards look for in protecting their CI/CD pipelines and processes.
ML model security is a moving target that demands scalable platforms
ML model threats will continue to accelerate as attackers seek to weaponize AI at every chance. The many vulnerabilities in software supply chains directly impact teams’ productivity, building ML models for release into production and broad use today.
JFrog’s approach of developing a platform that combines DevSecOps fundamentals to provide end-to-end vision and control of the ML models defines the future of secure software supply chains. Every CISO, Devops leader, and CEO is betting that ML model security must continue to evolve to stay current against threats, and platform architectures like JFrog’s re-defining how they secure ML models at scale is core to the future of secure software supply chains.
VentureBeat’s mission is to be a digital town square for technical decision-makers to gain knowledge about transformative enterprise technology and transact. Discover our Briefings.





